1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
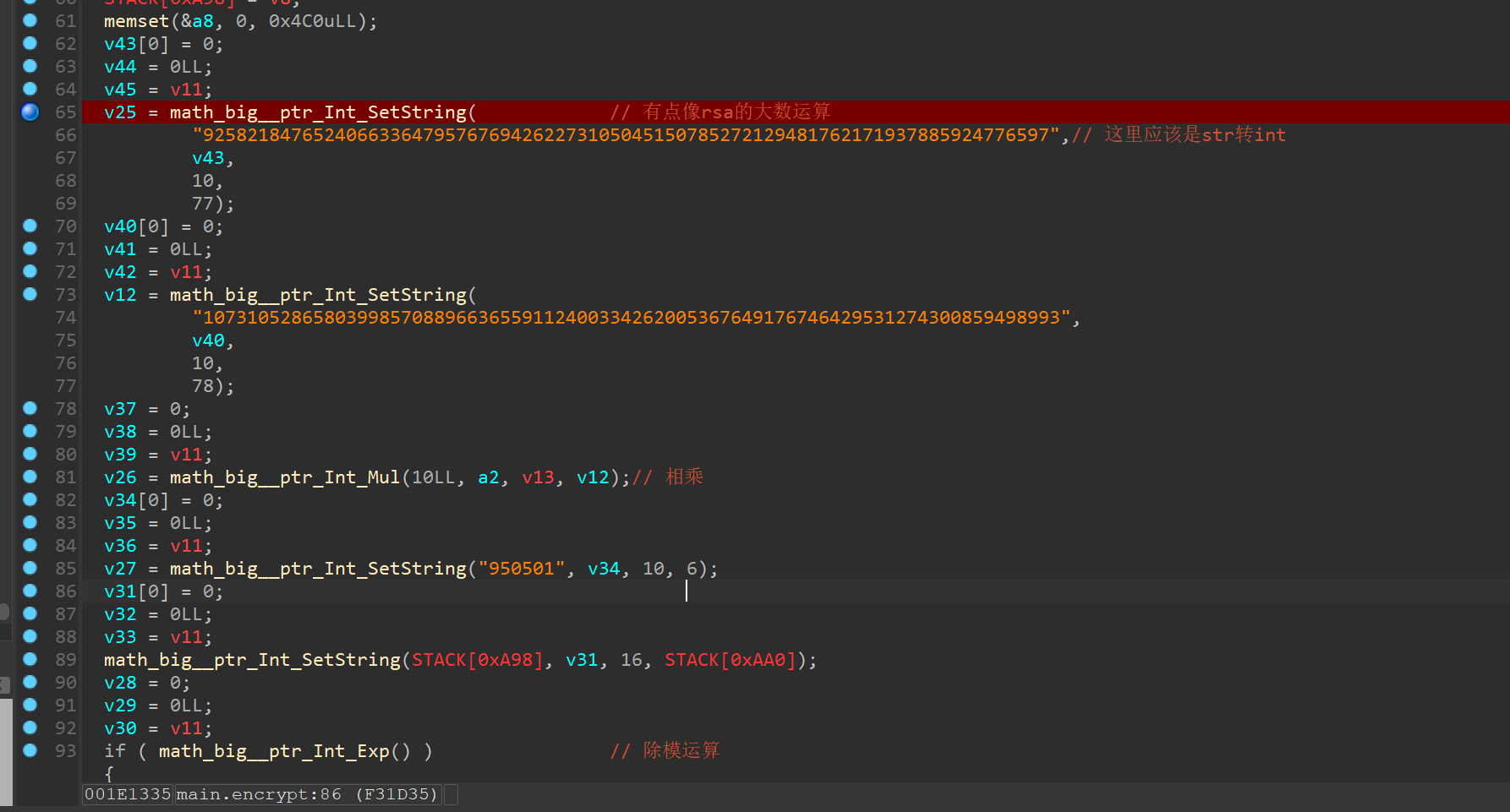
| import gmpy2
from Crypto.Util.number import long_to_bytes
q=92582184765240663364795767694262273105045150785272129481762171937885924776597
p=107310528658039985708896636559112400334262005367649176746429531274300859498993
data=[99, 85, 4, 3, 5, 5, 5, 3, 7, 7, 2, 8, 8, 11, 1, 2, 10, 4, 2, 13, 8, 9, 12, 9, 4, 13, 8, 0, 14,
0, 15, 13, 14, 10, 2, 2, 1, 7, 3, 5, 6, 4, 6, 7, 6, 2, 2, 5, 3, 3, 9, 6, 0, 11, 13, 11, 0, 2, 3, 8, 3, 11, 7, 1, 11, 5, 14, 5, 0, 10, 14, 15, 13, 7, 13, 7, 14, 1, 15, 1, 11, 5, 6, 2, 12, 6, 10, 4, 1, 7, 4, 2, 6, 3, 6, 12, 5, 12, 3, 12, 6, 0, 4, 15, 2, 14, 7, 0, 14, 14, 12, 4, 3, 4, 2, 0, 0, 2, 6, 2, 3, 6, 4, 4, 4, 7, 1, 2, 3, 9, 2, 12, 8, 1, 12, 3, 12, 2, 0, 3, 14, 3, 14, 12, 9, 1, 7, 15, 5, 7, 2, 2, 4]
e=950501
n=p*q
tmp=0x66
for i in range(1,153,2):
data[i] ^= tmp
tmp = data[i]
for j in range(40,56):
tmp=j
tmp ^= 0x66
cct=[i for i in data]
for i in range(0,153,2):
cct[i] ^= tmp
tmp = cct[i]
a=bytes(cct)
print(a)
enc=135005562109829034199059149474896341566307600227148289525068532297727897409776873250963225670468340868270979975367474527115512003915945795967599087720024
d=gmpy2.invert(e,(p-1)*(q-1))
m=pow(enc,d,n)
print(long_to_bytes(m))
|