hgame2022
hardend
安卓逆向,有点薄弱啊
试试
用jeb打开
看到bytecode的文件夹名称为secshell
检索一下,是邦邦加密
关于各种packer的lib名称
1 | "libchaosvmp.so":"娜迦", |
对文件进行脱壳

米家的跨屏协作还蛮好用
省去一些文件传输的繁琐
在540752的dex文件中捕捉到关键信息
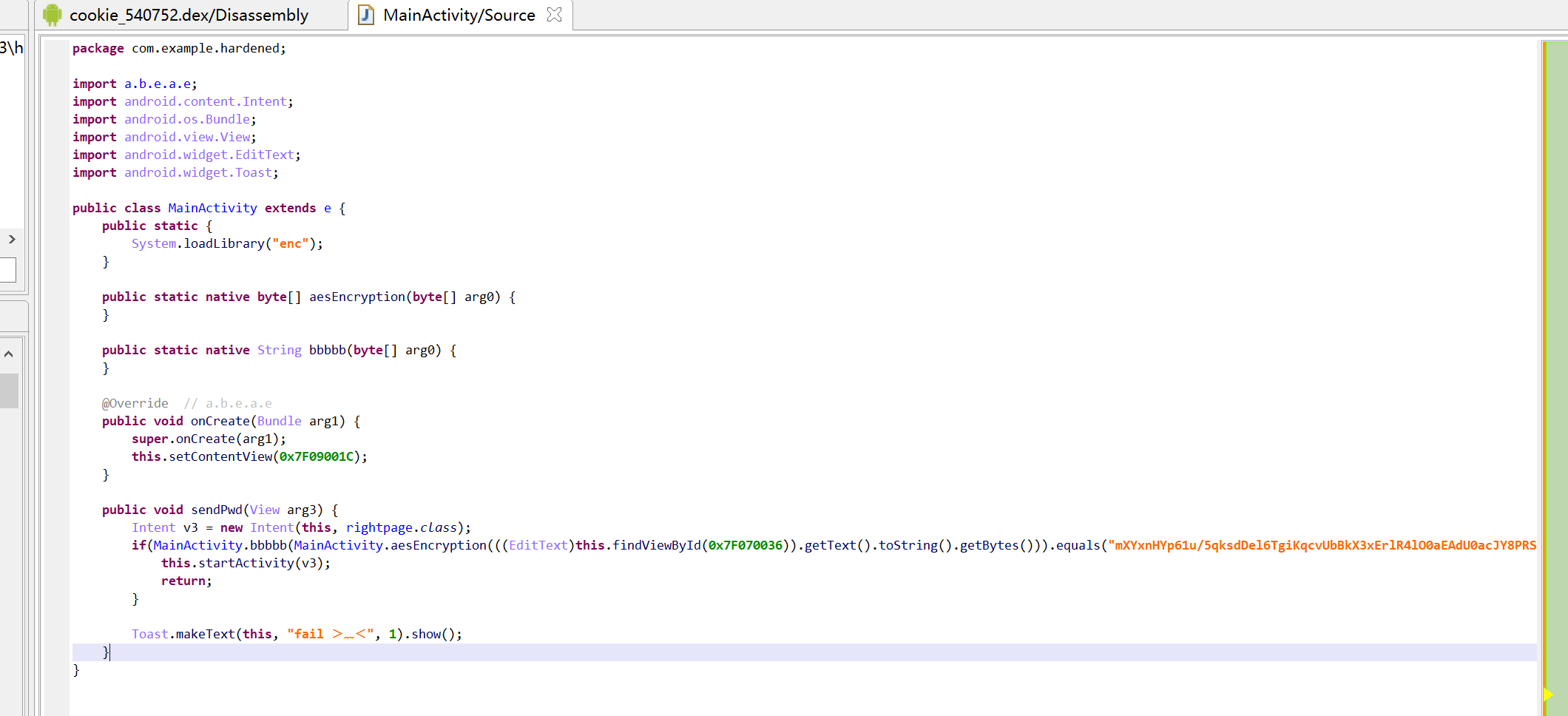
要匹配
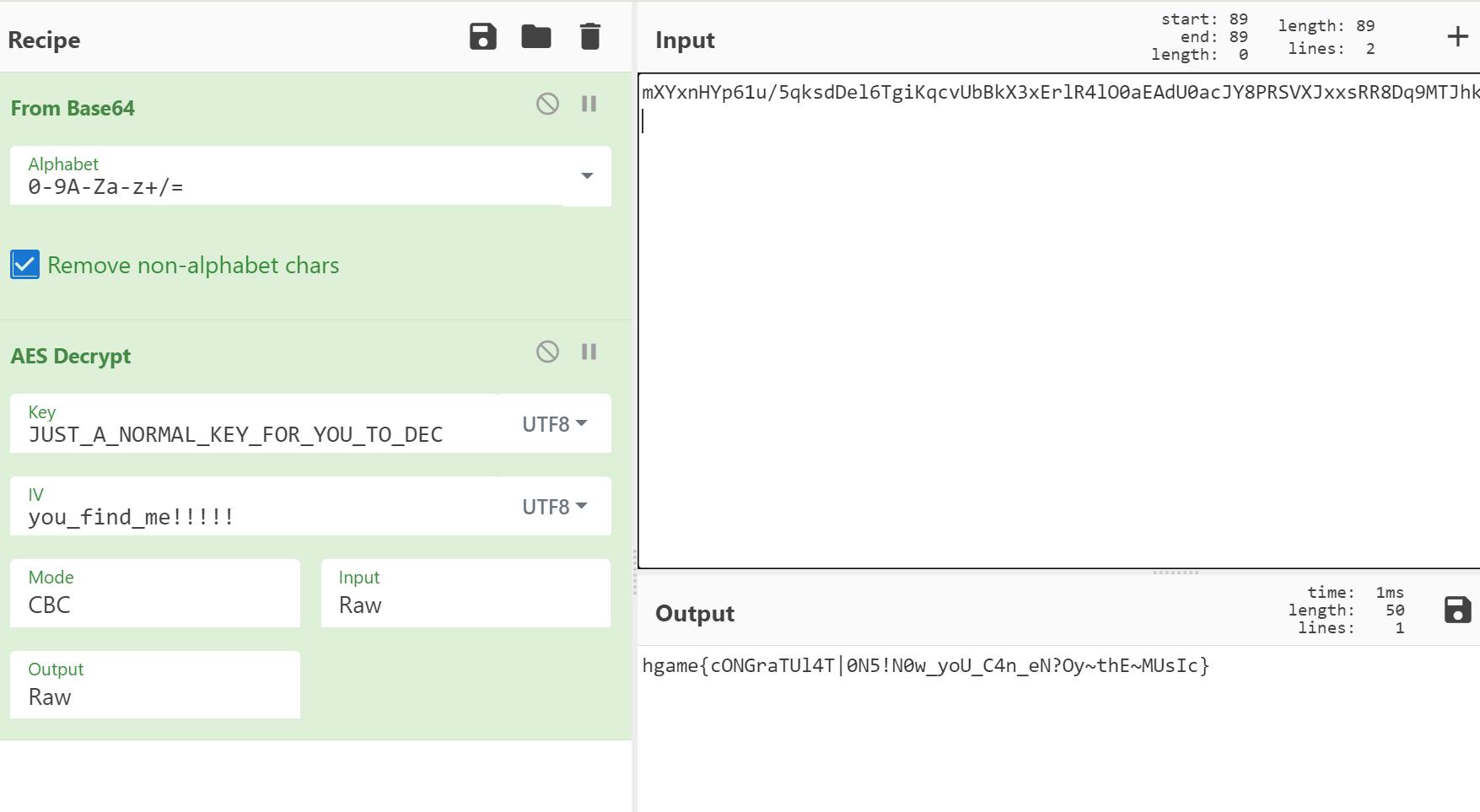
“mXYxnHYp61u/5qksdDel6TgiKqcvUbBkX3xErlR4lO0aEAdU0acJY8PRSVXJxxsRR8Dq9MTJhkWLSbBvCG5gtm==”
这段应该是base64的,不过应该是变表什么之类的,找找变表数据
这里上面调取了一个enc的库
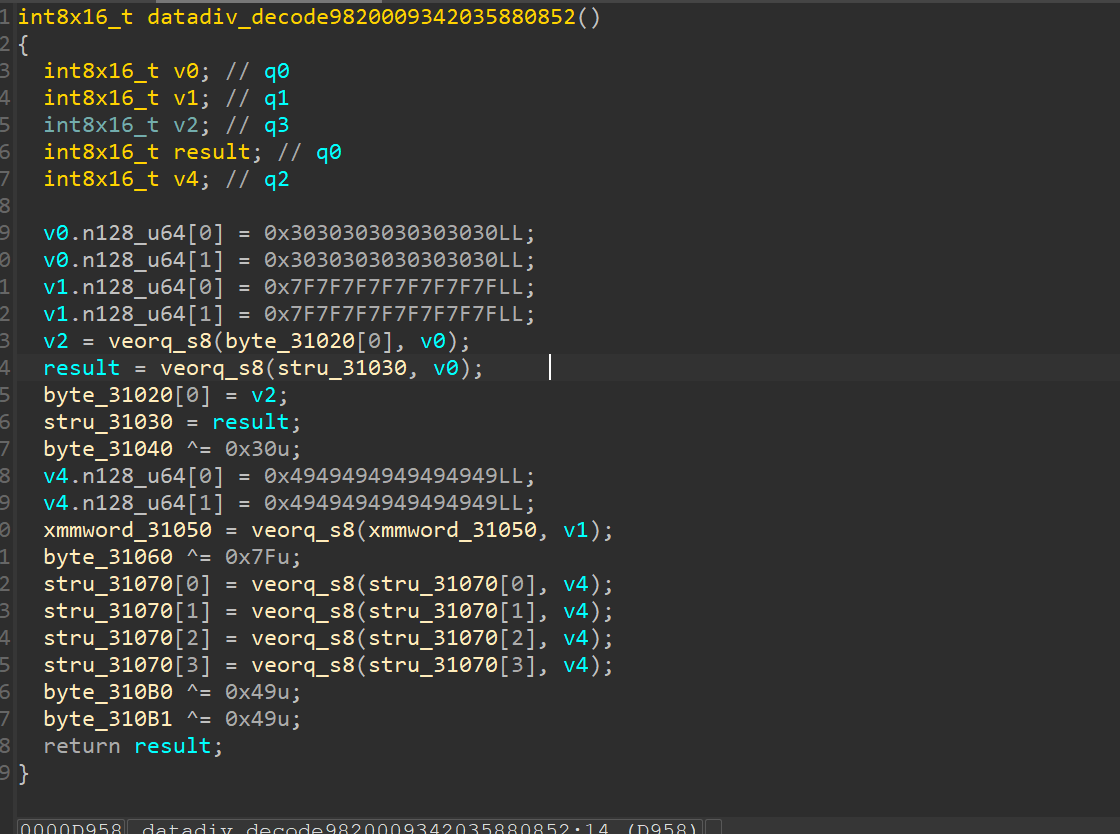
那就回到handened的解包文件中找到libenc.so
用ida64打开
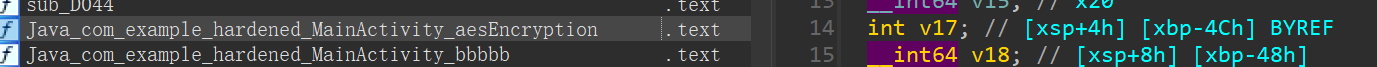
找到对应函数
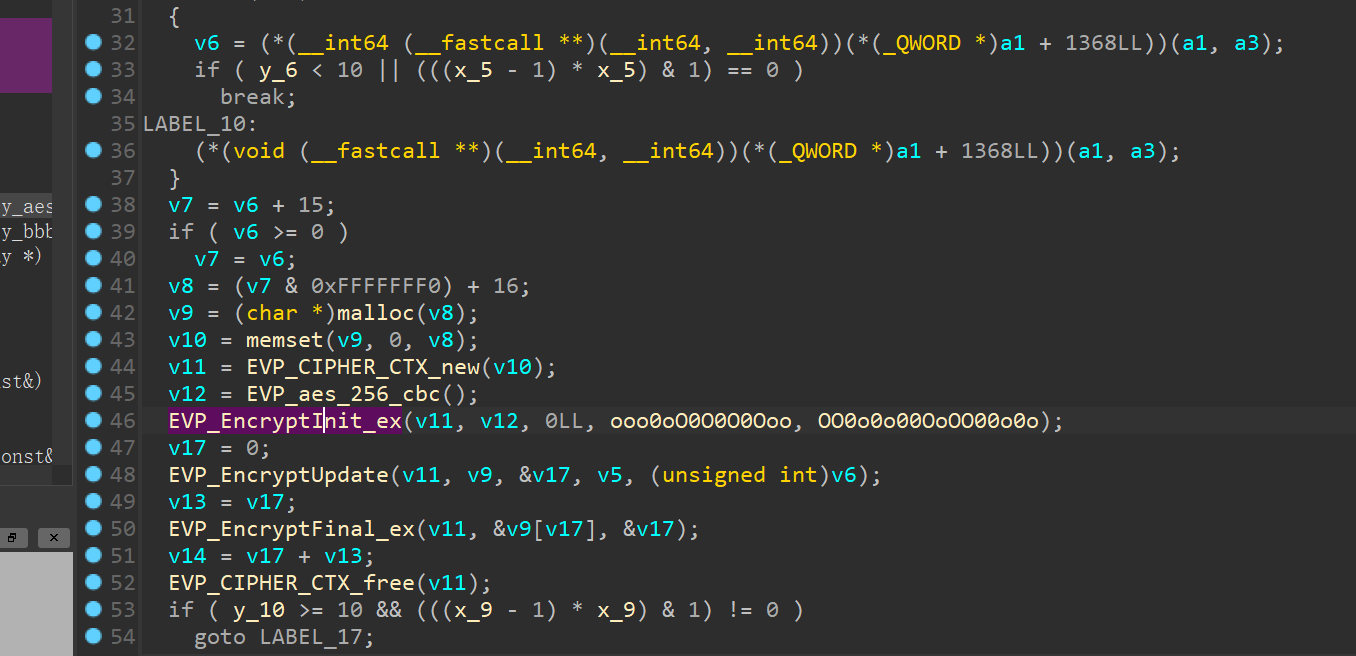
int EVP_EncryptInit_ex(EVP_CIPHER_CTX *ctx, const EVP_CIPHER *type,ENGINE *impl, unsigned char *key, unsigned char *iv);
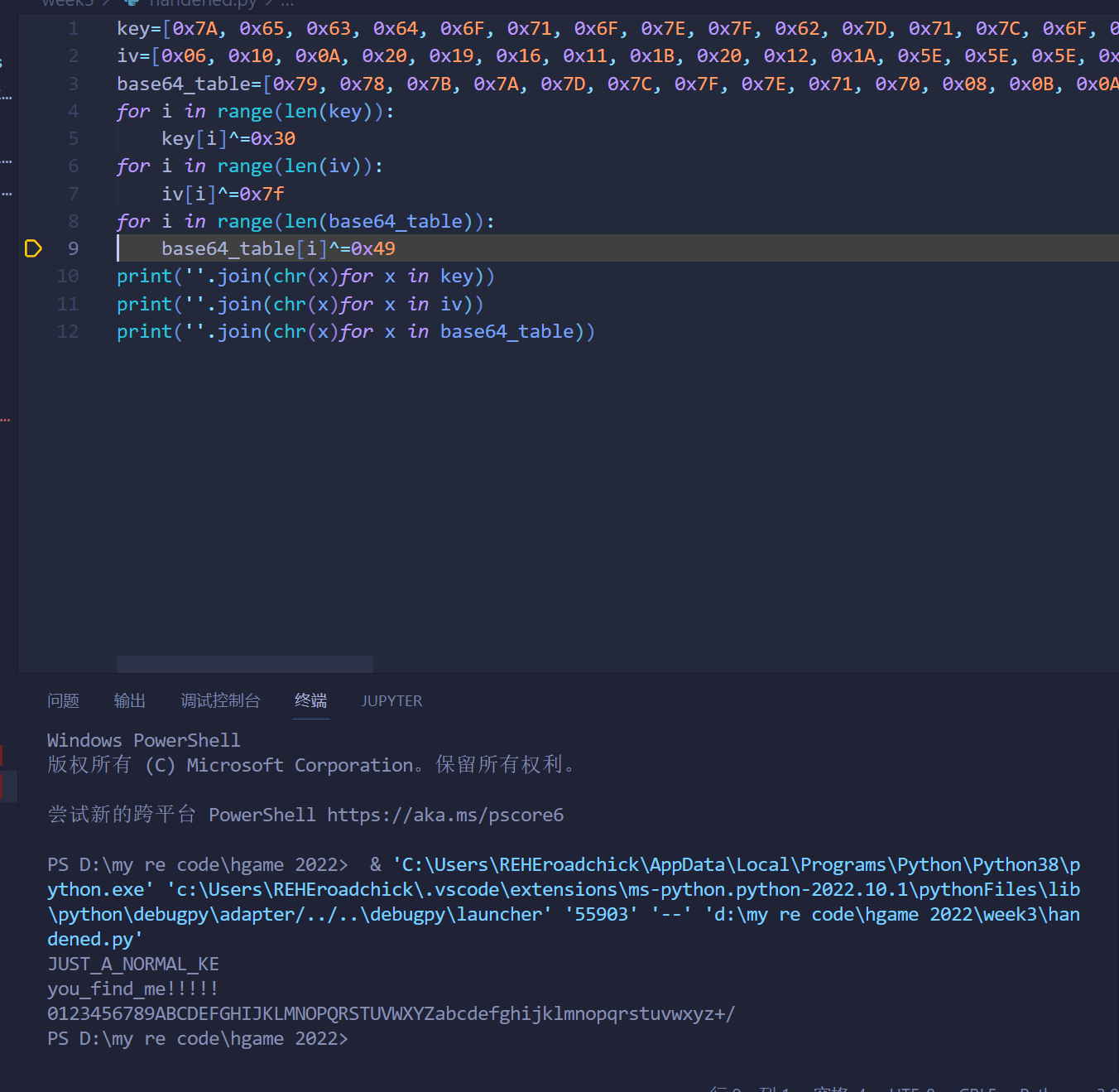
ooo 为key oo0为iv
base64特征
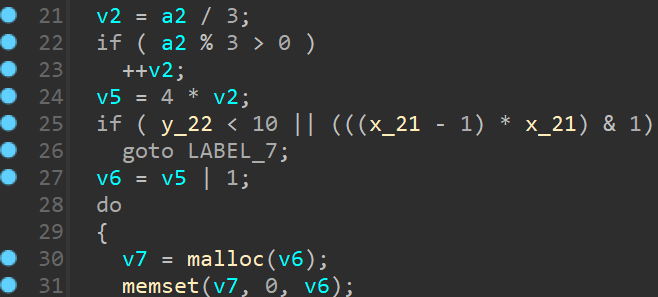
找找变表
交叉检索检索到变表位置
写个脚本
得出结果
得到aes模式的iv和key后
就可以
得出答案
本博客所有文章除特别声明外,均采用 CC BY-NC-SA 4.0 许可协议。转载请注明来自 kiki的博客!
