hgame2022
creakme3
这题是ppc(powerpc)逆向
我的ida似乎没有办法解析ppc
换成ida7.7就行
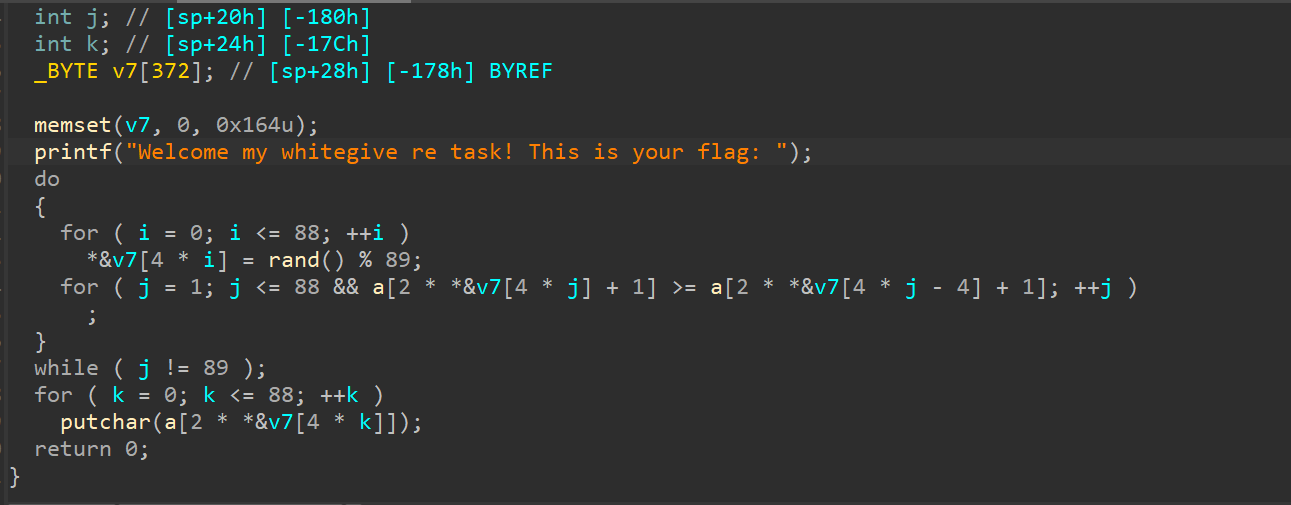
似乎是一个自输出flag的类型
看看怎么把它运行起来
仔细看看a里面的数据
似乎是要排序的
前面的小数据是阿斯卡码
后面的则是比较数据
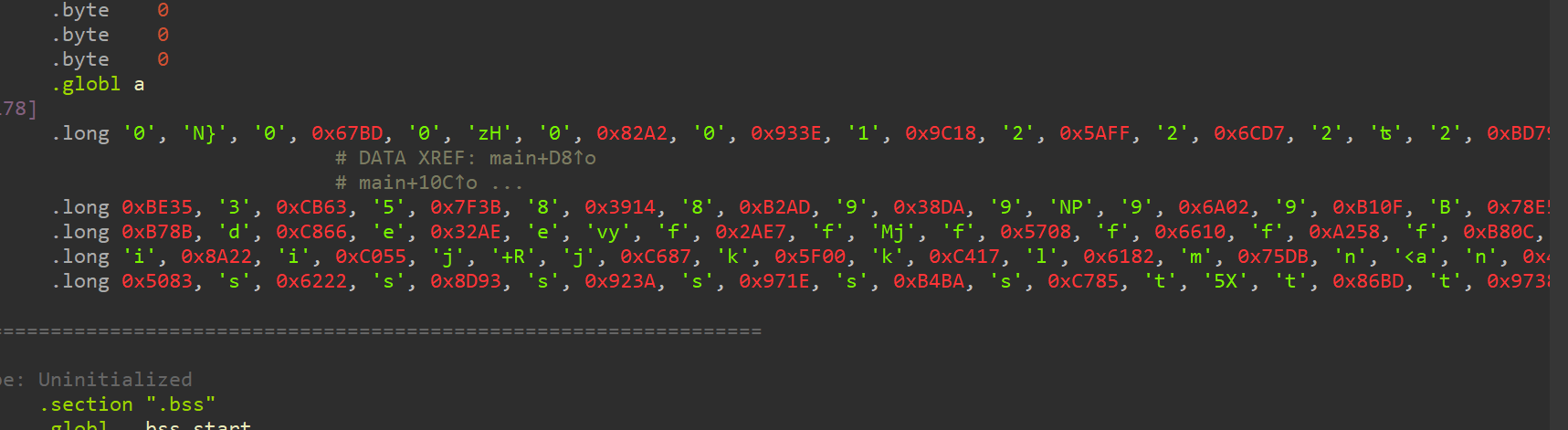
这里提取数据的时候还有一个大小端的问题
1 | data=[0x30000000, 0x7D4E0000, 0x30000000, 0xBD670000, 0x30000000, 0x487A0000, 0x30000000, 0xA2820000, 0x30000000, 0x3E930000, 0x31000000, 0x189C0000, 0x32000000, 0xFF5A0000, 0x32000000, 0xD76C0000, 0x32000000, 0xCAA60000, 0x32000000, 0x79BD0000, 0x32000000, 0xBDCE0000, 0x33000000, 0x4A320000, 0x33000000, 0x92320000, 0x33000000, 0x05390000, 0x33000000, 0x91420000, 0x33000000, 0xDE5A0000, 0x33000000, 0x9F6E0000, 0x33000000, 0x2AA50000, 0x33000000, 0x35BE0000, 0x33000000, 0x63CB0000, 0x35000000, 0x3B7F0000, 0x38000000, 0x14390000, 0x38000000, 0xADB20000, 0x39000000, 0xDA380000, 0x39000000, 0x504E0000, 0x39000000, 0x026A0000, 0x39000000, 0x0FB10000, 0x42000000, 0xE5780000, 0x5F000000, 0xF67E0000, 0x5F000000, 0xA3890000, 0x5F000000, 0xBD8E0000, 0x5F000000, 0xE3950000, 0x61000000, 0xDA730000, 0x64000000, 0x8C530000, 0x64000000, 0x3B630000, 0x64000000, 0x9C9E0000, 0x64000000, 0x8BB70000, 0x64000000, 0x66C80000, 0x65000000, 0xAE320000, 0x65000000, 0x79760000, 0x66000000, 0xE72A0000, 0x66000000, 0x6A4D0000, 0x66000000, 0x08570000, 0x66000000, 0x10660000, 0x66000000, 0x58A20000, 0x66000000, 0x0CB80000, 0x66000000, 0x85C80000, 0x67000000, 0x0A710000, 0x67000000, 0xF47C0000, 0x68000000, 0x763F0000, 0x68000000, 0x2B700000, 0x68000000, 0xEEA30000, 0x68000000, 0x50AD0000, 0x68000000, 0xC7BA0000, 0x69000000, 0x24400000, 0x69000000, 0x228A0000, 0x69000000, 0x55C00000, 0x6A000000, 0x522B0000, 0x6A000000, 0x87C60000, 0x6B000000, 0x005F0000, 0x6B000000, 0x17C40000, 0x6C000000, 0x82610000, 0x6D000000, 0xDB750000, 0x6E000000, 0x613C0000, 0x6E000000, 0x96490000, 0x6E000000, 0xC15D0000, 0x6F000000, 0x762D0000, 0x6F000000, 0x177D0000, 0x6F000000, 0x1BA90000, 0x70000000, 0xED9A0000, 0x72000000, 0xD0450000, 0x72000000, 0x67840000, 0x72000000, 0x5DAB0000, 0x73000000, 0x83500000, 0x73000000, 0x22620000, 0x73000000, 0x938D0000, 0x73000000, 0x3A920000, 0x73000000, 0x1E970000, 0x73000000, 0xBAB40000, 0x73000000, 0x85C70000, 0x74000000, 0x58350000, 0x74000000, 0xBD860000, 0x74000000, 0x38970000, 0x75000000, 0x10370000, 0x75000000, 0x79970000, 0x77000000, 0x3F2F0000, 0x77000000, 0xDD440000, 0x7B000000, 0xE1780000, 0x7D000000, 0x429F0000] |
收工
本博客所有文章除特别声明外,均采用 CC BY-NC-SA 4.0 许可协议。转载请注明来自 kiki的博客!
