b01lers 2022
b01lers
crackme
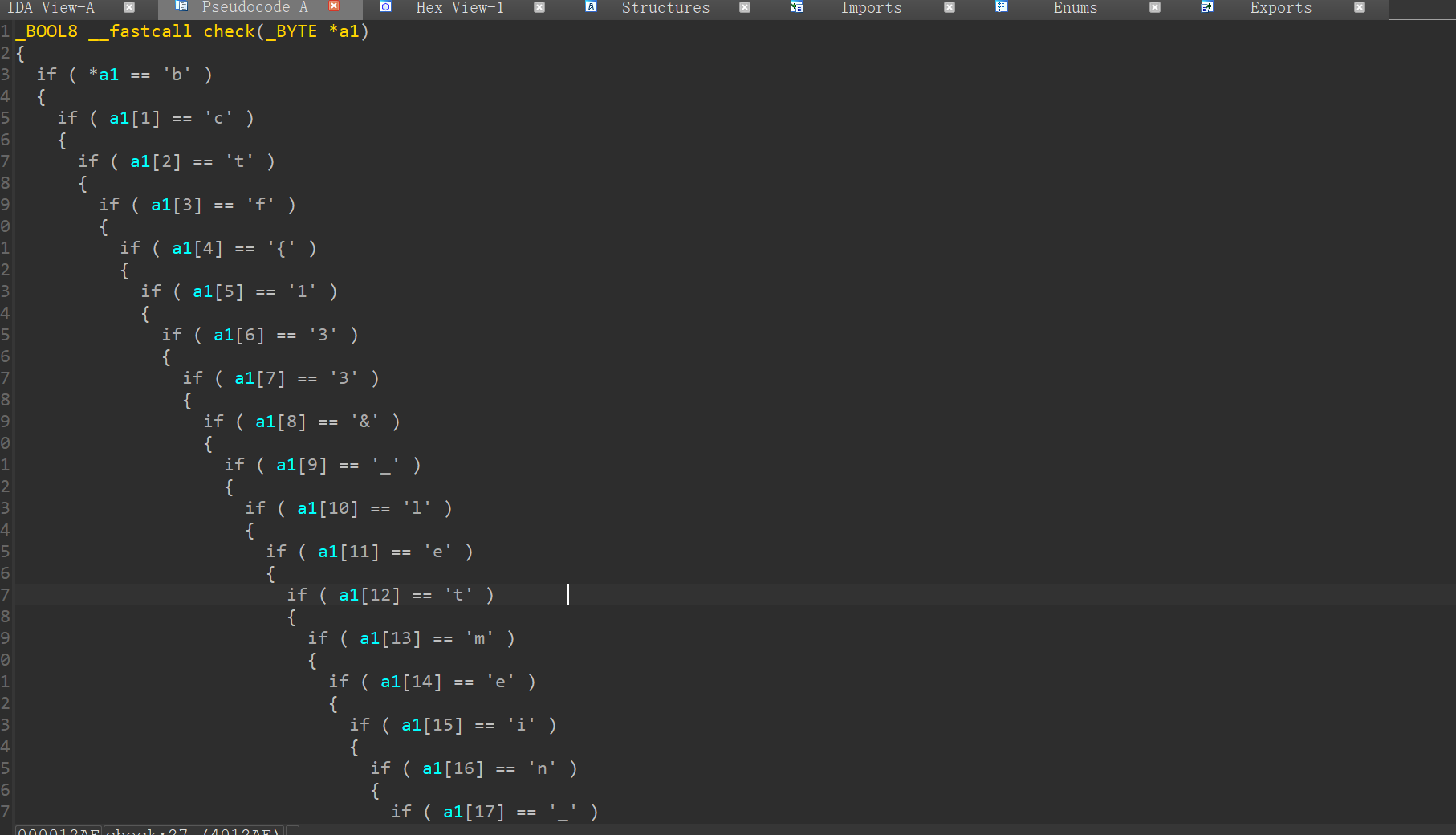
直接
bctf{133&_letmein_123}
crackme_2
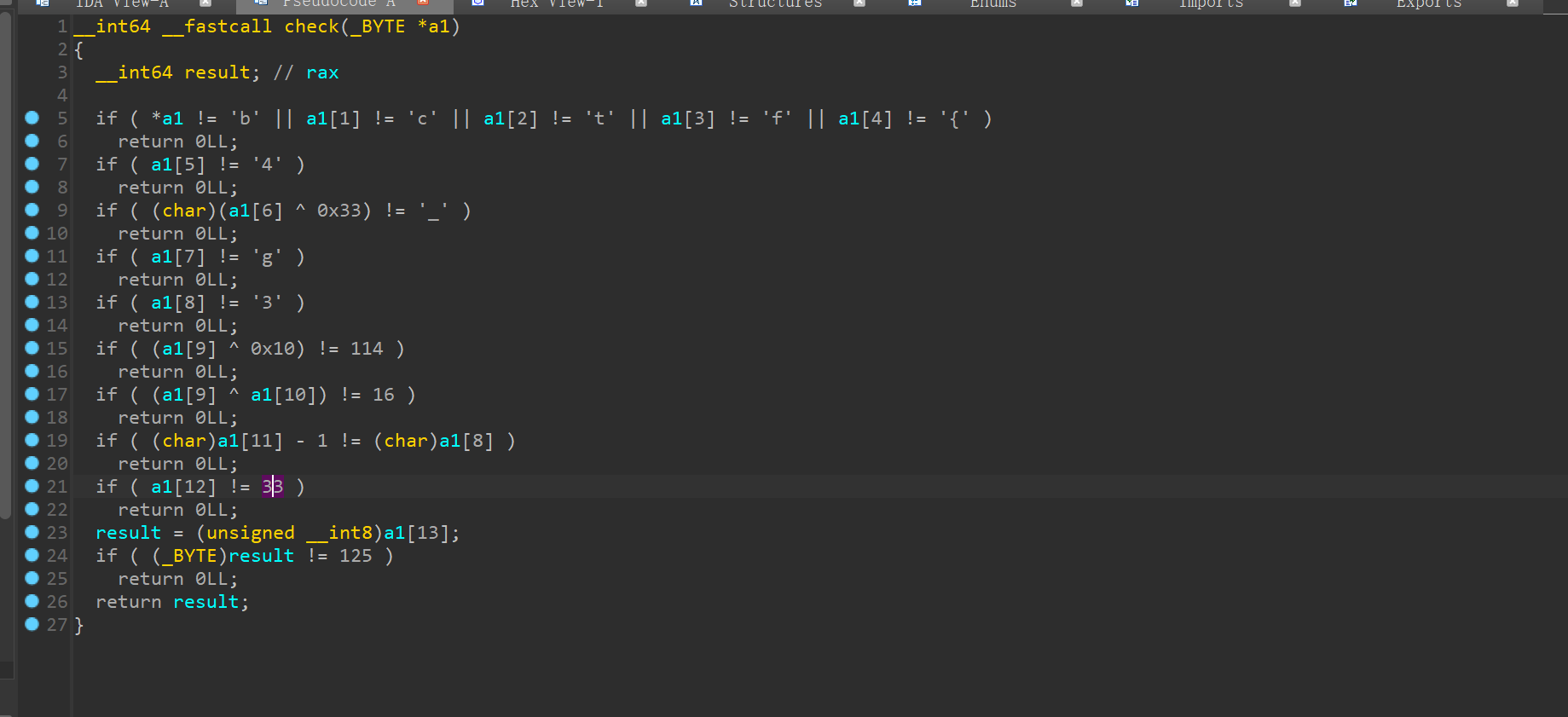
bctf{4lg3br4!}
extreme_64
这题是个汇编
nc ctf.b01lers.com 9301
查看服务器端口
1 | Warning: _curses.error: setupterm: could not find terminfo database |
I love JAVA
1 | /* |
中间有个java的随机数组
因为设置了seed所以可以还原出来
1 | import java.util.Random; |
忘记放脚本了www
1 | data=[116,122,54,50,93,66,98,117,75,51,97,78,104,119,90,53,94,36,105,84,40,69] |
bctf{J4V4_I$_th3_G04T}
extreme_64_part_2
又是另一道汇编题目
1 | Warning: _curses.error: setupterm: could not find terminfo database |
TM
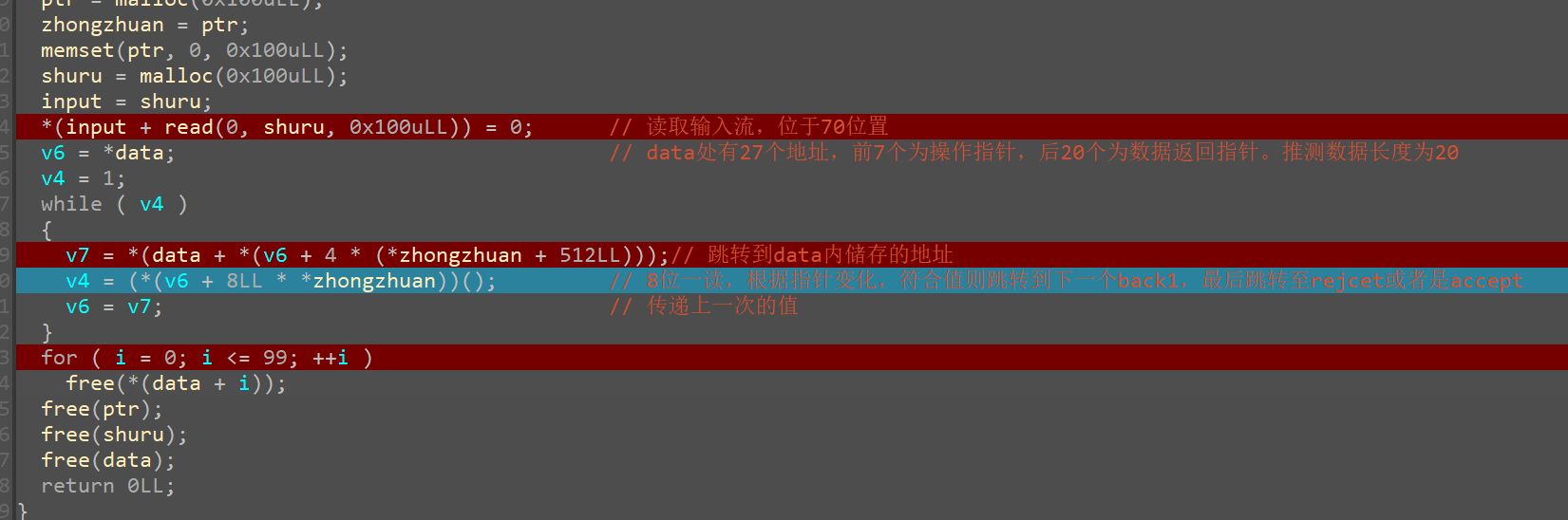
推测加密方式
所有值^0x45
偶数值+10,
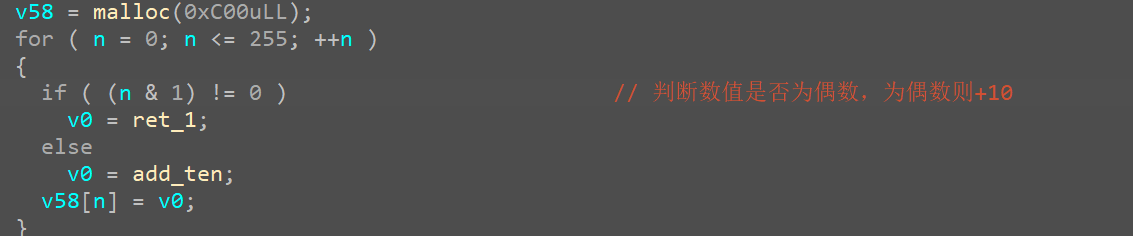
倒序检查
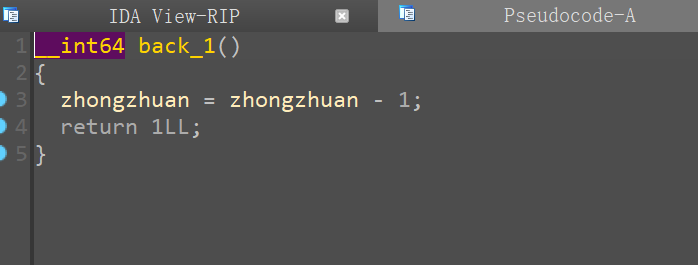
指针位置
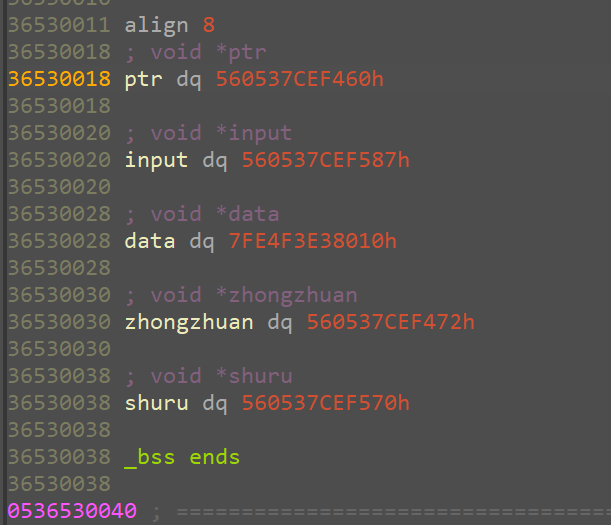
几个不同的指针,分辨指向不同的状态
data内部的地址
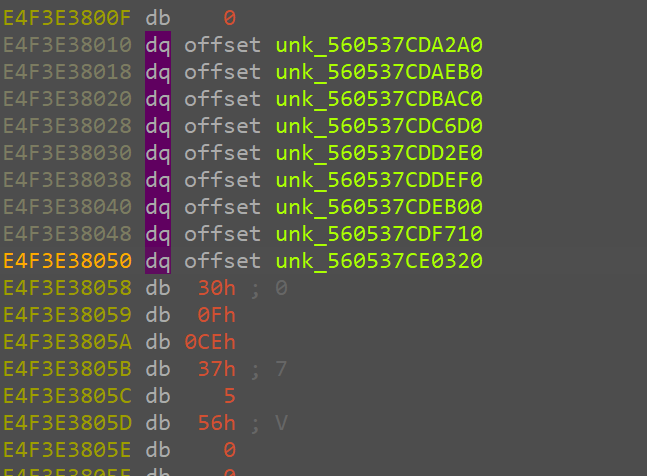
其中前面7个都是指向不同操作的,分别是传输input,数据加法,数据异或,和轮空。
而后20位则都是back1,进行数据比较
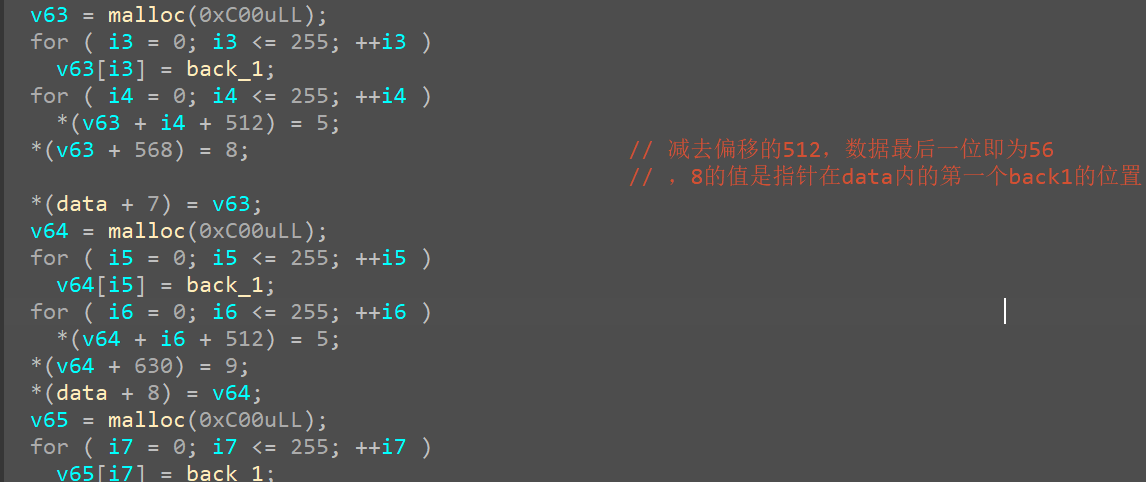
不过至于为什么是这个结构。。
似乎ida对结构体编译的不是很好
1 | encode1=[0x29, 0x26, 0x3B, 0x35, 0x3E, 0x3B, 0x30, 0x39, 0x74, 0x3D, |
bctf{tur1ng_m4_C_1n3}
ps:这题我还以为是按照数据的值来进行指针跳转。。。实际上我是看8,9,10递增看出来的。。。网上的wp看不懂啦,英文不会啦,日文不会啦,韩文不会啦,俄文不会啦wwww
本博客所有文章除特别声明外,均采用 CC BY-NC-SA 4.0 许可协议。转载请注明来自 kiki的博客!
