1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
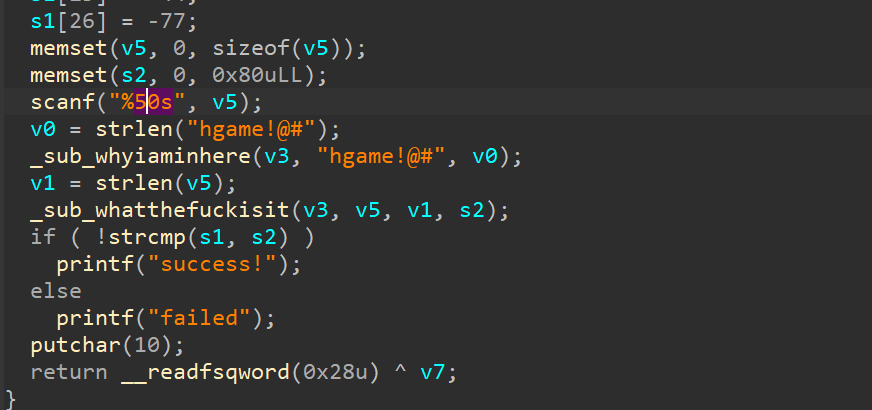
| #include<stdio.h>
#include<string.h>
typedef unsigned longULONG;
void rc4_init(unsigned char* s, unsigned char* key, unsigned long Len)
{
int i = 0, j = 0;
char k[256] = { 0 };
unsigned char tmp = 0;
for (i = 0; i < 256; i++)
{
s[i] = i;
k[i] = key[i % Len];
}
for (i = 0; i < 256; i++)
{
j = (j + s[i] + k[i]) % 256;
tmp = s[i];
s[i] = s[j];
s[j] = tmp;
}
}
void rc4_crypt(unsigned char* s, unsigned char* Data, unsigned long Len)
{
int i = 0, j = 0, t = 0;
unsigned long k = 0;
unsigned char tmp;
for (k = 0; k < Len; k++)
{
i = (i + 1) % 256;
j = (j + s[i]) % 256;
tmp = s[i];
s[i] = s[j];
s[j] = tmp;
t = (s[i] + s[j]) % 256;
Data[k] ^= s[t];
}
}
int main()
{
unsigned char s[256] = { 0 }, s2[256] = { 0 };
char key[256] = {"hgame!@#"};
char pData[512] = {67, 36, 229, 161, 197, 29, 114, 210, 40, 239, 190, 234, 165, 151, 68, 96, 217, 15, 44, 111, 94, 38, 179, 10, 252, 212, 179};
int i;
unsigned long len = strlen(pData);
rc4_init(s, (unsigned char*)key, strlen(key));
for (i = 0; i < 256; i++)
{
s2[i] = s[i];
}
rc4_crypt(s2, (unsigned char*)pData, len);
printf("answer= %s\n\n", pData);;
return 0;
}
|