1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
|
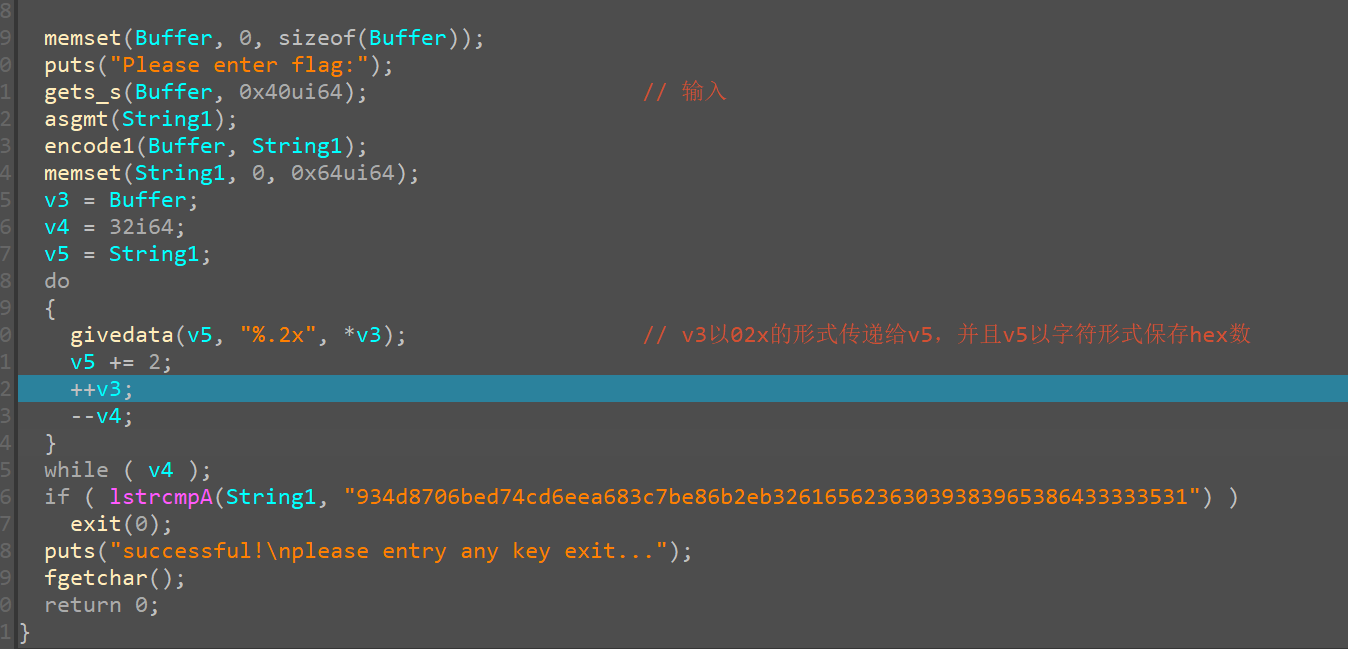
import threading
data2='934d8706bed74cd6eea683c7be86b2eb32616562363039383965386433333531'
string1=[0x1B, 0x2E, 0x35, 0x46, 0x58, 0x6E, 0x72, 0x86, 0x9B, 0xA7, 0xB5, 0xC8, 0xD9, 0xEF, 0xFF, 0x0C, 0xC5, 0x38, 0xCB, 0x73,
0x9D, 0x56, 0xB9, 0xF5, 0x06, 0xF1, 0x0C, 0x3D, 0xDF, 0x1E,0xF3, 0x31, 0xB5, 0x35, 0x0C, 0xED, 0x28, 0x63, 0xB5, 0x18,
0x2E, 0x92, 0xB9, 0x25, 0xF1, 0x8C, 0x4A, 0x14, 0xD5, 0xE3,0xF6, 0x4C, 0xFD, 0x80, 0x43, 0x54, 0xD3, 0x12, 0xFA, 0x71,
0x22, 0x9E, 0xB0, 0x65, 0xD6, 0x04, 0xBB, 0xDF, 0x2B, 0x84, 0xF8, 0x8B, 0xF8, 0x96, 0x02, 0xFA, 0xDA, 0x08, 0xB2, 0x9F,
0xF6, 0x33, 0x60, 0x88, 0xDD, 0xB7, 0x98, 0x03, 0x25, 0x21, 0x9A, 0xF9, 0xFF, 0x29, 0x28, 0x66, 0x73, 0x07, 0x53, 0x9E,
0xAE, 0xB0, 0xCB, 0x9D, 0x8B, 0x91, 0x51, 0x64, 0x74, 0xB8,0x79, 0x02, 0x5F, 0xB1, 0x24, 0x0C, 0xF1, 0x01, 0xEF, 0x91,
0x7A, 0x90, 0xBE, 0xF5, 0x0E, 0x28, 0xC7, 0xF7, 0xEB, 0x77,0x4C, 0xA7, 0x1A, 0x76, 0xA3, 0x36, 0x60, 0xE6, 0x1D, 0xC3,
0x6E, 0xCE, 0xDA, 0x34, 0x7B, 0x20, 0x54, 0x38, 0x61, 0x56,0xF7, 0x0E, 0x01, 0xB0, 0xEA, 0xCD, 0x6F, 0x7E, 0x30, 0xF9,
0xBE, 0x24, 0xCD, 0x90, 0xDF, 0x72, 0x3A, 0x9E, 0xDE, 0xC2,0xD0, 0x53, 0xB1, 0xBC, 0xE0, 0xAA, 0x02, 0x00, 0x00, 0x00,
0x00, 0x00, 0x00, 0x00, 0xEE, 0x17, 0x14, 0x8A, 0xF7, 0x7F, 0x00, 0x00]
data4=[0x63, 0x7C, 0x77, 0x7B, 0xF2, 0x6B, 0x6F, 0xC5, 0x30, 0x01, 0x67, 0x2B, 0xFE, 0xD7, 0xAB, 0x76, 0xCA, 0x82, 0xC9, 0x7D
, 0xFA, 0x59, 0x47, 0xF0, 0xAD, 0xD4, 0xA2, 0xAF, 0x9C, 0xA4, 0x72, 0xC0, 0xB7, 0xFD, 0x93, 0x26, 0x36, 0x3F, 0xF7, 0xCC,
0x34, 0xA5, 0xE5, 0xF1, 0x71, 0xD8, 0x31, 0x15, 0x04, 0xC7, 0x23, 0xC3, 0x18, 0x96, 0x05, 0x9A, 0x07, 0x12, 0x80, 0xE2
, 0xEB, 0x27, 0xB2, 0x75, 0x09, 0x83, 0x2C, 0x1A, 0x1B, 0x6E, 0x5A, 0xA0, 0x52, 0x3B, 0xD6, 0xB3, 0x29, 0xE3, 0x2F, 0x84,
0x53, 0xD1, 0x00, 0xED, 0x20, 0xFC, 0xB1, 0x5B, 0x6A, 0xCB, 0xBE, 0x39, 0x4A, 0x4C, 0x58, 0xCF, 0xD0, 0xEF, 0xAA, 0xFB,
0x43, 0x4D, 0x33, 0x85, 0x45, 0xF9, 0x02, 0x7F, 0x50, 0x3C, 0x9F, 0xA8, 0x51, 0xA3, 0x40, 0x8F, 0x92, 0x9D, 0x38, 0xF5,
0xBC, 0xB6, 0xDA, 0x21, 0x10, 0xFF, 0xF3, 0xD2, 0xCD, 0x0C, 0x13, 0xEC, 0x5F, 0x97, 0x44, 0x17, 0xC4, 0xA7, 0x7E, 0x3D,
0x64, 0x5D, 0x19, 0x73, 0x60, 0x81, 0x4F, 0xDC, 0x22, 0x2A, 0x90, 0x88, 0x46, 0xEE, 0xB8, 0x14, 0xDE, 0x5E, 0x0B, 0xDB,
0xE0, 0x32, 0x3A, 0x0A, 0x49, 0x06, 0x24, 0x5C, 0xC2, 0xD3, 0xAC, 0x62, 0x91, 0x95, 0xE4, 0x79, 0xE7, 0xC8, 0x37, 0x6D,
0x8D, 0xD5, 0x4E, 0xA9, 0x6C, 0x56, 0xF4, 0xEA, 0x65, 0x7A, 0xAE, 0x08, 0xBA, 0x78, 0x25, 0x2E, 0x1C, 0xA6, 0xB4, 0xC6,
0xE8, 0xDD, 0x74, 0x1F, 0x4B, 0xBD, 0x8B, 0x8A, 0x70, 0x3E, 0xB5, 0x66, 0x48, 0x03, 0xF6, 0x0E, 0x61, 0x35, 0x57, 0xB9,
0x86, 0xC1, 0x1D, 0x9E, 0xE1, 0xF8, 0x98, 0x11, 0x69, 0xD9, 0x8E, 0x94, 0x9B, 0x1E, 0x87, 0xE9, 0xCE, 0x55, 0x28, 0xDF,
0x8C, 0xA1, 0x89, 0x0D, 0xBF, 0xE6, 0x42, 0x68, 0x41, 0x99, 0x2D, 0x0F, 0xB0, 0x54, 0xBB]
def paixu (decode1):
copy=[]
for x in decode1:
copy.append(x)
decode1[5]=copy[1]
decode1[10]=copy[2]
decode1[15]=copy[3]
decode1[9]=copy[5]
decode1[14]=copy[6]
decode1[3]=copy[7]
decode1[13]=copy[9]
decode1[2]=copy[10]
decode1[7]=copy[11]
decode1[1]=copy[13]
decode1[6]=copy[14]
decode1[11]=copy[15]
def jiansuo (deccode1):
for i in range(16):
for a in range(len(data4)):
if data4[a]==deccode1[i]:
deccode1[i]=a
break
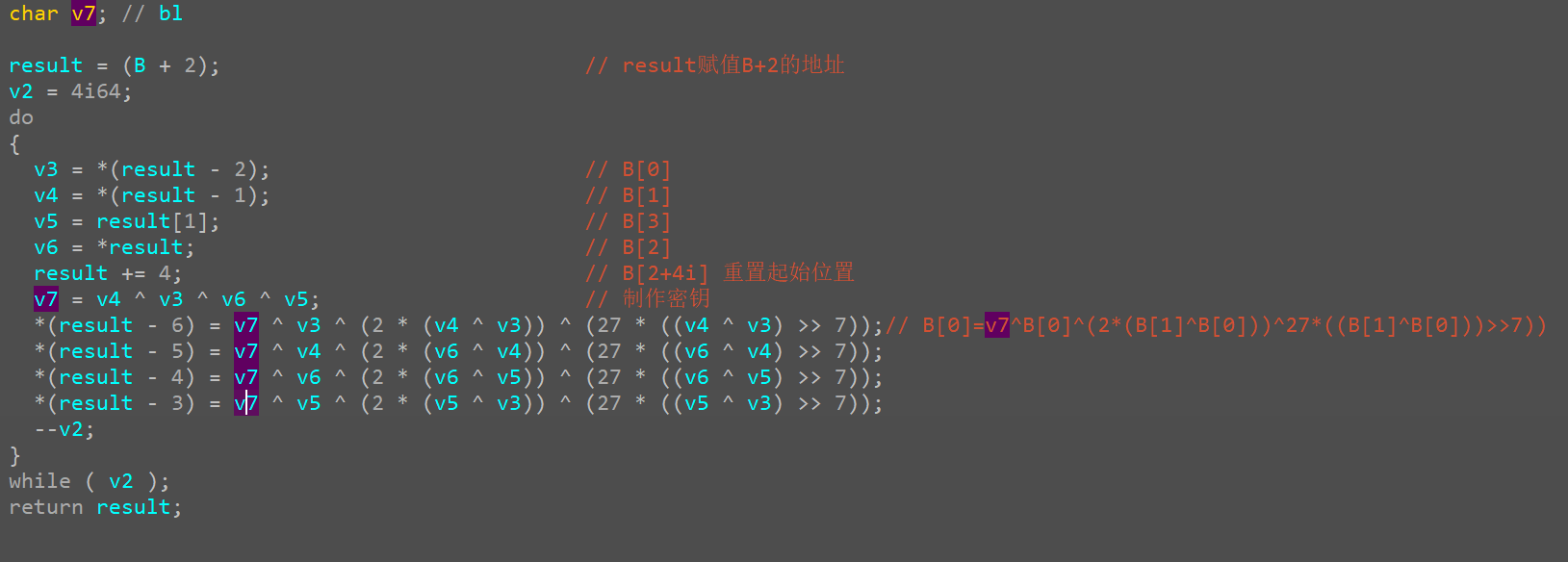
def decode0 (decode1):
print("start!")
for v3 in range(0,255):
for v4 in range(0,255):
for v6 in range(0, 255):
for v5 in range(0, 255):
v7=v4^v3^v6^v5
if decode1[0] == (v7 ^ v3 ^ (2 * (v4 ^ v3)) ^ (27 * ((v4 ^ v3) >> 7)))&0xff and decode1[1] ==( v7 ^ v4 ^ (2 * (v6 ^ v4)) ^ (27 * ((v6 ^ v4) >> 7)))&0xff and decode1[2] == (v7 ^ v6 ^ (2 * (v6 ^ v5)) ^ (27 * ((v6 ^ v5) >> 7)))&0xff and decode1[3] == (v7 ^ v5 ^ (2 * (v5 ^ v3)) ^ (27 * ((v5 ^ v3) >> 7)))&0xff:
decode1[0]=v3
decode1[1]=v4
decode1[2]=v6
decode1[3]=v5
return print("next!")
def decode2 (decode1):
print("running now!")
for v3 in range(0,255):
for v4 in range(0,255):
for v6 in range(0, 255):
for v5 in range(0, 255):
v7=v4^v3^v6^v5
if decode1[0] == (v7 ^ v3 ^ (2 * (v4 ^ v3)) ^ (27 * ((v4 ^ v3) >> 7)))&0xff and decode1[1] ==( v7 ^ v4 ^ (2 * (v6 ^ v4)) ^ (27 * ((v6 ^ v4) >> 7)))&0xff and decode1[2] == (v7 ^ v6 ^ (2 * (v6 ^ v5)) ^ (27 * ((v6 ^ v5) >> 7)))&0xff and decode1[3] == (v7 ^ v5 ^ (2 * (v5 ^ v3)) ^ (27 * ((v5 ^ v3) >> 7)))&0xff:
decode1[4]=v3
decode1[5]=v4
decode1[6]=v6
decode1[7]=v5
return print("next!")
def decode3 (decode1):
for v3 in range(0,255):
for v4 in range(0,255):
for v6 in range(0, 255):
for v5 in range(0, 255):
v7=v4^v3^v6^v5
if decode1[0] == (v7 ^ v3 ^ (2 * (v4 ^ v3)) ^ (27 * ((v4 ^ v3) >> 7)))&0xff and decode1[1] ==( v7 ^ v4 ^ (2 * (v6 ^ v4)) ^ (27 * ((v6 ^ v4) >> 7)))&0xff and decode1[2] == (v7 ^ v6 ^ (2 * (v6 ^ v5)) ^ (27 * ((v6 ^ v5) >> 7)))&0xff and decode1[3] == (v7 ^ v5 ^ (2 * (v5 ^ v3)) ^ (27 * ((v5 ^ v3) >> 7)))&0xff:
decode1[8]=v3
decode1[9]=v4
decode1[10]=v6
decode1[11]=v5
return
def decode4 (decode1):
print("end!")
for v3 in range(0,255):
for v4 in range(0,255):
for v6 in range(0, 255):
for v5 in range(0, 255):
v7=v4^v3^v6^v5
if decode1[0] == (v7 ^ v3 ^ (2 * (v4 ^ v3)) ^ (27 * ((v4 ^ v3) >> 7)))&0xff and decode1[1] ==( v7 ^ v4 ^ (2 * (v6 ^ v4)) ^ (27 * ((v6 ^ v4) >> 7)))&0xff and decode1[2] == (v7 ^ v6 ^ (2 * (v6 ^ v5)) ^ (27 * ((v6 ^ v5) >> 7)))&0xff and decode1[3] == (v7 ^ v5 ^ (2 * (v5 ^ v3)) ^ (27 * ((v5 ^ v3) >> 7)))&0xff:
decode1[12]=v3
decode1[13]=v4
decode1[14]=v6
decode1[15]=v5
return
def decode ():
thread1=threading.Thread( decode0(decode1))
thread2=threading.Thread( decode2(decode1))
thread3=threading.Thread( decode3(decode1))
thread4=threading.Thread(decode4(decode1))
thread1.start()
thread2.start()
thread3.start()
thread4.start()
print(len(string1))
data2_l=list(data2)
decode1=[]
double=data2_l[::2]
single=data2_l[1::2]
for i in range(len(double)):
a=ord(double[i])
if a<=57 and a>=48:
a-=48
else:
a=a-87
double[i]=a
a=ord(single[i])
if a<=57 and a>=48:
a-=48
else:
a=a-87
single[i]=a
c=double[i]*16+single[i]
decode1.append(c)
data=''
for x in decode1:
data+=chr(x)
print(data)
for i in range(16):
decode1[i] = (decode1[i] ^ string1[160 + i]) & 0xff
paixu(decode1)
jiansuo(decode1)
for x in range(9):
for i in range(16):
decode1[i] = (decode1[i] ^ string1[(9-x)*16 + i]) & 0xff
decode()
paixu(decode1)
jiansuo(decode1)
for i in range(16):
decode1[i] = (decode1[i]^string1[i])&0xff
flag=''
for x in decode1:
flag+=chr(x)
print(flag)
|